Microsoft recently published a data mentioning how many machines (users) were affected by ransomware attacks across the world. It was found that the United States was on the top of ransomware attacks; followed by Italy and Canada. Here are the top 20 countries which are majorly affected by ransomware attacks.
Here is a detailed write-up that will answer most of your questions regarding ransomware. This post will take a look at What are Ransomware Attacks, the Types of ransomware, How does ransomware gets on your computer and suggests ways of dealing with ransomware.
Ransomware attacks explained
What is Ransomware
Ransomware is a type of malware that locks your files, data or the PC itself and extorts money from you in order to provide access. This is a new way for malware writers to ‘collect funds’ for their illegitimate activities on the web.
How does ransomware get on your computer
You could get ransomware if you click on a bad link or open a malicious email attachment. This image from Microsoft describes how the ransomware infection takes place.
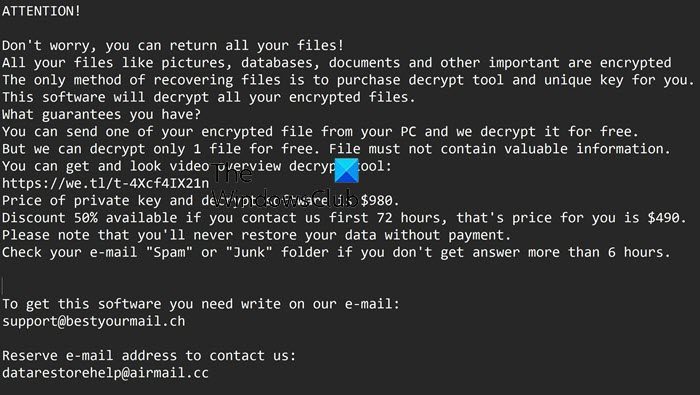
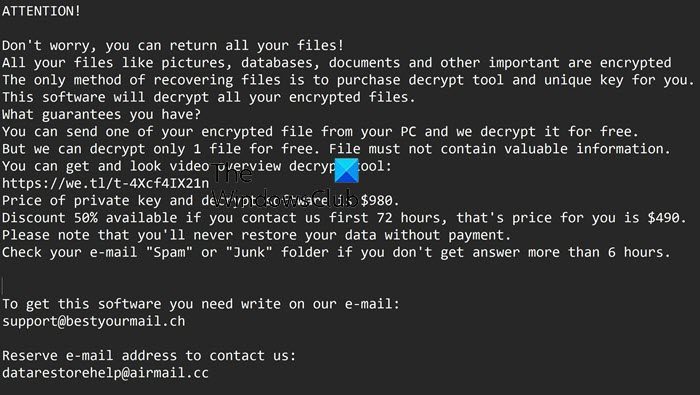
Ransomware looks like an innocent program or a plugin or an email with a ‘clean’ looking attachment that gets installed without the user’s knowledge. As soon as it gets its access to the user’s system, it starts spreading across the system. Finally, at one point of time, the ransomware locks the system or particular files and restricts the user from accessing it. Sometimes, these files are encrypted. A ransomware writer demands a certain amount of money to provide access or decrypt the files. A fake warning message by a ransomware looks as follows:
However, during the ransomware attacks, there is no guarantee that the users will get back their files even after paying the ransom. Hence, it is better to prevent ransomware attacks than trying to get back your data from some way or another. You may use RanSim Ransomware Simulator to check if your computer is sufficiently protected. Read: What to do after a Ransomware attack on your Windows computer?
How to identify ransomware attacks
The ransomware generally attacks the personal data, such as user’s pictures, documents, files, and data. It is easy to identify the ransomware. If you see a ransomware note demanding money to give access to your files, or encrypted files, renamed files, locked browser or a locked screen of your PC, you can say that ransomware has got a grip on your system.
However, the symptoms of ransomware attacks can change as per the types of ransomware. Read: Malware Tracker Maps that let you view Cyber Attacks in real-time.
Types of ransomware attacks
Earlier, ransomware used to display a message stating that the user has done something illegal and they are being fined by the police or the government agency on the basis of some policy. To get rid of these ‘charges’ (which were definitely false charges), users were asked to pay these fines. Nowadays, a ransomware attack in two ways. It either locks the computer screen or encrypts certain files with a password. Based on these two types, the ransomware is divided into two types: Lock screen ransomware locks your system and demands a ransom for letting you access it once again. The second type, i.e. the Encryption ransomware, changes the files in your system and demands money to decrypt them again. The other types of ransomware are:
Who can be affected by the ransomware attacks
It doesn’t matter where you are and what device you are using. Ransomware can attack anybody, anytime and anywhere. The ransomware attacks can take place on any mobile device, PC or laptop when you are using the internet for surfing, emailing, working, or shopping online. Once it finds a way to your mobile device or the PC, it will employ its encryption and monetization strategies into that PC and mobile device.
When can ransomware get a chance to attack
So what are the possible events when ransomware can strike?
If you are browsing untrusted websitesDownloading or opening file attachments received from unknown email senders (spam emails). Some of the file extensions of these attachments can be, (.ade, .adp, .ani, .bas, .bat, .chm, .cmd, .com, .cpl, .crt, .hlp, .ht, .hta, .inf, .ins, .isp, .job, .js, .jse, .lnk, .mda, .mdb, .mde, .mdz, .msc, .msi, .msp, .mst, .pcd, .reg, .scr, .sct, .shs, .url, .vb, .vbe, .vbs, .wsc, .wsf, .wsh, .exe, .pif.) And also he file types that support macros (.doc, .xls, .docm, .xlsm, .pptm, etc.)Installing pirated software, outdated software programs or operating systemsLogging into a PC that is a part of the already infected network
Precautions against ransomware attacks
The only reason ransomware is created, is because the malware writers see it as an easy way to make money. Vulnerabilities such as unpatched software, outdated operating systems or people’s ignorance is beneficial for such people with malicious and criminal intentions. Hence, awareness is the best way to avoid any attacks by ransomware. Here are are a few steps you can take to tackle or deal with ransomware attacks: The Ransomware Tracker helps you track, mitigate and protect yourself from malware. Read: Protect against and prevent Ransomware attacks. While there are some ransomware decryptor tools available, it is advisable that you take the problem of ransomware attacks seriously. It not only endangers your data, but it can also breach your privacy to such extent that it can harm your reputation also. Says Microsoft, If you do happen to have the misfortune of being infected with ransomware, you can if you wish, report Ransomware to FBI, Police or appropriate authorities. Now read about Ransomware protection in Windows.